
“Zero Trust” Supports Remote Work
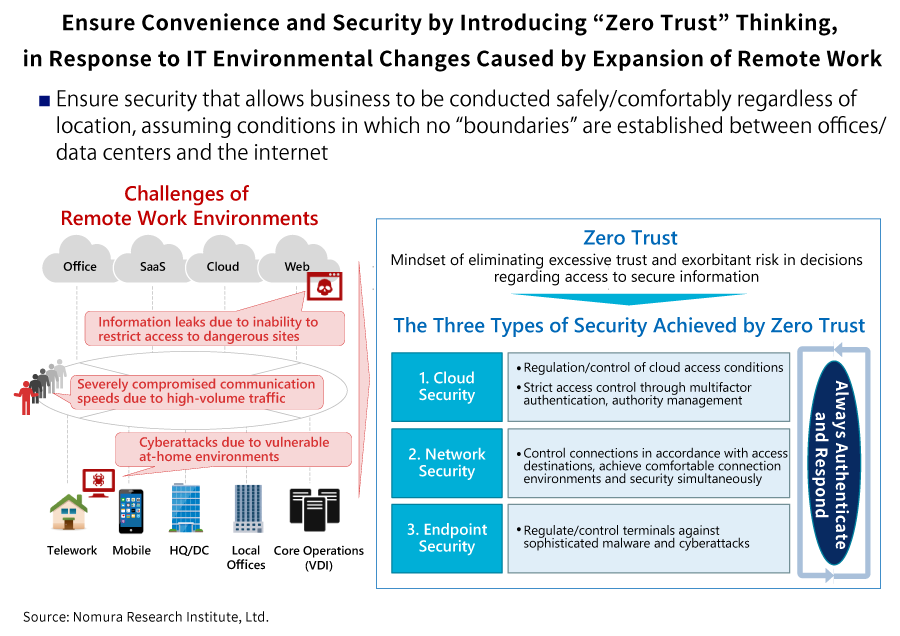
The number of companies making use of remote work has been on the rise during the coronavirus pandemic, but the realization and spread of these practices demand security environments that allow business to be conducted safely and comfortably regardless of location. By now, it has become clear that the increase in remote work introduces many problems, including greater risk of exposure to information leaks and cyberattacks, and reduced communication speeds due to high-volume traffic. We discussed the “zero trust” security concept, which is attracting attention as a solution to these problems, with Shinya Ishii of NRI SecureTechnologies and Isao Eguchi and Go Oono of Nomura Research Institute (NRI), all of are experts with a wealth of practical knowledge and experience about these issues.
Why zero trust now?
Fundamentally, the internet is a system based on the view that human beings are inherently good. Its purpose is connection, and it has evolved to allow computers to connect to each other simply. As a result, any malicious person with technical skill can put together a cyberattack without much trouble. This means that when companies connect to the internet, they must protect their internal information assets by creating a barrier, called a firewall, between their internal networks and the outside internet. Under this mentality, which seeks to protect the barrier between inside and outside because inside is safe and outside is dangerous, any access to internal networks that is permitted will be trusted regardless of circumstances. This is the foundation of conventional network security.
However, this approach introduces the risk that if malware-infected mobile PCs, USBs, etc. are brought into a company, the infection will spread throughout internal networks easily. The same thing can happen if even one internal device is infected by malware in an email attachment. With the expansion of remote work, external access to internal resources is increasing, but this trend creates various problems, including the impossibility of responding when weaknesses in the VPN gateways used for internal access are exploited to infiltrate internal networks. This is why attention has begun to focus on security policies premised on the idea of “trust no one (Zero Trust)”, regardless of whether the connection is internal or external.
The model for this zero trust approach has been around for about 20 years, but the term “zero trust” was coined in 2010 by John Kindervag of Forrester Research, an investigation firm in the United States. The idea has reentered the spotlight in recent years, against a backdrop of expanding remote work and an increasingly vague boundary between internal and external. Unlike the era when internal data stayed internal, more and more companies today are storing more and more of their data and applications in the cloud, causing a proliferation of areas that may be vulnerable to attack. With the spread of remote work, there has been an extreme increase in traffic that passes over networks from external to internal sources and then back outside again, and the construction of security rooted in zero trust thinking is becoming a common objective from the standpoint of suppressing this phenomenon as well.
The Three Types of Security Achieved with Zero Trust
A security policy based on zero trust gets rid of the preconception that internal networks are safe, and instead, always evaluates all access without differentiating internal from external. More specifically, suspicious access that would not be caught by a firewall alone is detected and regulated through the addition of systems in which, whenever there is an access request, the identity of the user and security state of the terminal are authenticated, and access to the relevant information assets is granted on the basis of predefined conditions.
There are three key locations in this process: an “endpoint” such as a PC or mobile device; a “cloud” where applications and data are stored; and a “network” that connects the other two. By utilizing solutions etc. that can simultaneously realize device regulation/control for malware and cyberattacks at the endpoints, regulation/control of access conditions and multifactor authentication in the cloud, and comfortable connection environments and security on the network, this approach creates optimal and safe environments for the companies that adopt it.
But we don’t want people to misunderstand: incorporating a zero trust approach does not mean introducing completely new security solutions. Its purpose is to eliminate excessive trust and exorbitant risk in companies, and to ensure convenience and security. Therefore, depending on a company’s business and characteristics, if strengthening IT infrastructure is not currently an objective, it is also possible to incorporate zero trust concepts by, for example, revising existing network policies and rules to reduce the risk and impact of cyberattacks. Likewise, for companies that anticipate an expansion of telework or cloud utilization going forward, it is necessary to combine various solutions, including zero trust network access (ZTNA), and consider the optimal solution for the organization.
Towards the introduction of zero trust
When introducing zero trust, it is essential to review both hard aspects of security such as infrastructure, and soft aspects of security such as governance and rules. If you can create a zero-trust-based IT infrastructure, the convenience of your work environment will be significantly enhanced for the users, including by allowing them to engage in remote work and utilize the cloud. At the same time, however, these advances always go hand in hand with risks and threats from the company perspective. It is essential that, while providing IT infrastructure environments, companies also establish rules, stipulate acceptable modes of use, and otherwise cooperate with divisions in charge of governance.
NRI Group is home to security experts in the endpoint, cloud, and security fields, and prides itself on offering, realizing, and supporting solutions tailored to the work styles of its clients. NRI also offers security consulting, including for the establishment of governance structures. Our aim is to grow together with our clients, by having them share their goals and then providing support all the way through to introduction, including by offering application for the demands of clients’ environments and grand designs aimed at realizing their vision for the future, and assisting with policy formulation. Through these activities, we also hope that we can contribute, however slightly, to the advancement and refinement of social infrastructures that will realize safety and stability.
Profile
-
Shinya Ishii
-
Isao Eguchi
-
Go Oono
* Organization names and job titles may differ from the current version.